INI Students Defend CMU Hacking Team's Title at MITRE Cybersecurity Competition
By Ryan Noone
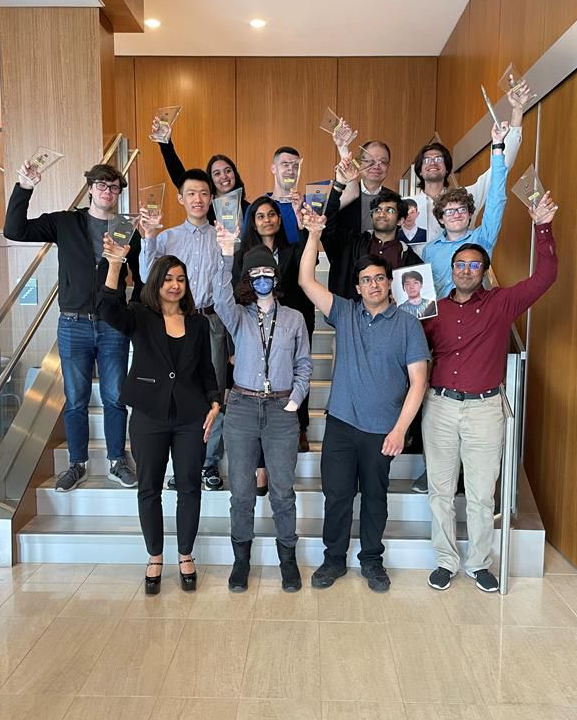
Media InquiriesFor the second year in a row, Carnegie Mellon’s competitive hacking team, the Plaid Parliament of Pwning (PPP), has taken home the top prize at the MITRE Embedded Capture-the-Flag (eCTF) cybersecurity competition. The PPP team is made up of 14 students from across the university, more than half of which were INI students and alumni. INI Associate Teaching Professor Patrick Tague serves as a co-advisor to the team while Assistant Teaching Professor Hanan Hibshi serves as a faculty advisor.
"CTF competitions are more than just games. The challenges help players enhance the essential skills that make them more valuable in the workplace,” said Dr. Dena Haritos Tsamitis, director of the INI and Barbara Lazarus Professor of Information Networking. “I am thrilled to see such a high level of participation from our INI community and wanted to congratulate the PPP team members, as well as the faculty advisors who continue to dedicate themselves to training the problem solvers of the future.”
"Participating in the MITRE eCTF was one of the most enlightening experiences I’ve had. "
Aditya Desai (MSIS '34)
Over the course of three months, PPP, and 79 other collegiate-level teams, worked to design and implement a key fob system for a car door lock to prevent unauthorized entry or attacks such as replays and key fob cloning.
PPP’s win was definitive, scoring over 10,000 points more than the second-place finisher. CyLab Security and Privacy Institute Project Scientist Maverick Woo, who co-advised the team with Electrical and Computer Engineering (ECE) Professor Anthony Rowe and Tague, credits the victory to the group’s composition and work ethic.
“Our team has strong expertise in both embedded development and attacks,” said Woo. “Our students worked hard and were committed, and they were able to organize themselves to take advantage of the large team size.”
The annual competition saw teams from the United States and around the world, with a record-breaking 546 student participants. Notably, PPP finished ahead of hackers from the University of California, Santa Cruz (2nd place), and the University of Illinois Urbana-Champaign (3rd place).
"In this competition, I was able to apply what I had learned and design and implement our own secure protocol from scratch."
Nandan Desai (MSIS '34)
The competition had two phases—design and attack. Each phase offered opportunities to score points by obtaining flags and submitting them to the live eCTF scoreboard.
During the design phase, hackers acted as a team of engineers at a car manufacturer, designing and building the embedded software that would be installed on the next line of cars and key fobs sold to customers. In the attack phase, teams had the opportunity to analyze other groups’ designs and identify security flaws as they aimed to unlock and start the vehicles without authorization from the vehicle owners.
"I needed a bit of prodding to sign up for the team, but ultimately, I'm incredibly glad I did. Being able to work with some of the smartest people at CMU was a priviledge, and I learned a lot from them as well as the experience at large."
Harrison Leinweber (MSIS '34)
eCTF competitions are unique from other CTF competitions because they focus on embedded systems security. Students not only defend against traditional cybersecurity attack vectors but also need to consider hardware-based attacks such as side-channel attacks, fault injection attacks and hardware modification attacks.