CMU crowned hacking champs for fifth time in seven years
Five INI students and alums were part of PPP's winning team at DefCon's 'World Series of Hacking'
By Daniel Tkacik
& Jessica Shirley
Carnegie Mellon University’s competitive hacking team, the Plaid Parliament of Pwning (PPP), just won its fifth hacking world championship in seven years at this year’s DefCon security conference, widely considered the “World Cup” of hacking. The championship, played in the form of a virtual game of “capture the flag,” was held August 8-11 in Las Vegas.
PPP now holds two more DefCon titles than any other team in the 23-year history of DefCon hosting the competition.
says David Brumley, a professor of Electrical and Computer Engineering at Carnegie Mellon, and the faculty advisor to the team.“If you’re wondering who the best and brightest security experts in the world are, look no further than the capture the flag room at DefCon,”
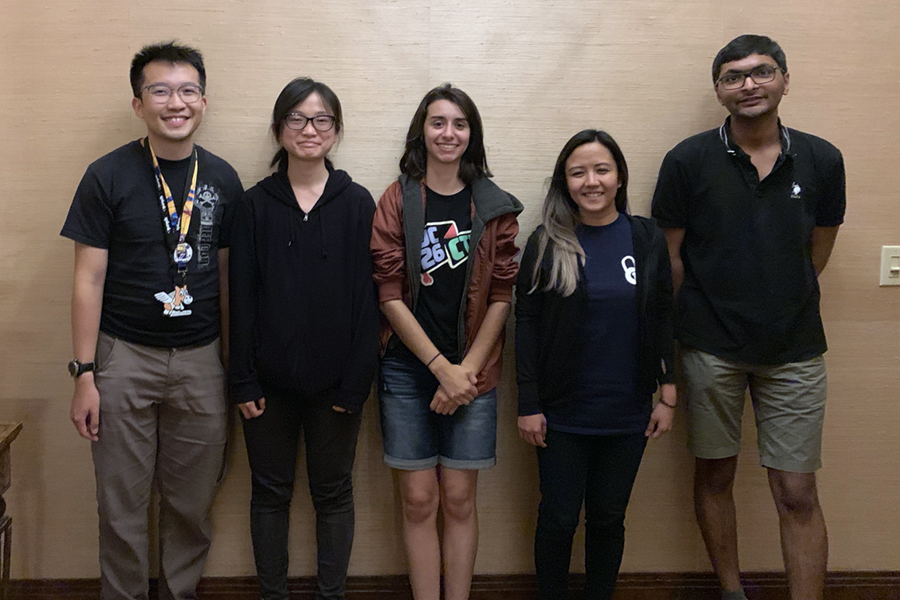
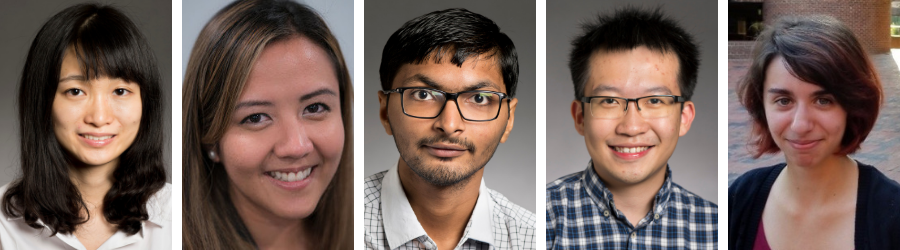
Five students and alumnae of the Information Networking Institute (INI) competed on PPP's winning team at DefCon27: current INI students Susie Chang (MS30), Jenish Rakholiya (MS30), and Wai Tuck Wong (MS30); and INI alumnae Erye Hernandez (MS24) and Carolina Zarate (MS29).
Three of the five biggest data breaches ever have occurred in the past 12 months, leaking nearly 2 billion personal records. For security experts trying to defend against these types of attacks, the annual DefCon conference provides an opportunity to hone their skills and practice on one another.
"As the top hacking competition in the world, DefCon is the best place to learn the latest and greatest tactics in security," said Zarate, a recent graduate of the INI’s integrated master's program in information security and a three-time competitor at DefCon. "The CTF is meant to test you with the wildest puzzles and the craziest techniques. Yes, you lose a lot of sleep but it's really worth it in the end."
"These competitions are so much more than just games," added Zach Wade, a student in Carnegie Mellon’s School of Computer Science and one of PPP’s team captains. "They bring together the security community to share and test new ideas that can be used to strengthen the security of the systems and devices we use every day."
Over the course of the 72-hour hacking spree, teams made up of students, industry workers, and government contractors attempted to break into each other’s systems, stealing virtual “flags” and accumulating points. This year's competition involved serveral different operating systems and architecture, and aside from the more traditional-style challenges, there was an iOS application, machine learning challenge, an Xbox game and a Lisp machine. To add drama, team scores were hidden from view on the second day, and scores and rankings were hidden on the last day, sending teams into a hacking frenzy.
"This year, we were particularly in the zone for the challenges and our teamwork was very on point," said Zarate. She says the team's camaraderie is an essential aspect of their success, and sums up the 72+ hour experience as involving "(mostly) goofing off, not sleeping, and maybe a little hacking with friends."
"PPP inspires me to learn, do and grow," said fellow PPP teammate Chang.
The 2019 competition consisted of 16 pre-qualified teams with members from at least seven countries around the world. Team “HITCONxBfKin” from Taiwan placed second overall, with team “Tea Deliverers” from China trailing in third.
The PPP team was made up of 22 students and alumni drawn from across Carnegie Mellon's departments and colleges. This year, the team had four female competitors.
"Diversity in cybersecurity, especially on a CTF team, offers advantages because successfully solving such complex challenges requires individuals with different skillsets and diverse perspectives," said Dr. Dena Haritos Tsamitis, director of the INI. "I'm proud to see Carnegie Mellon's commitment to increasing representation in computing and engineering reflected on PPP."
The Carnegie Mellon hacking team first formed in 2009 and began competing at DefCon in 2010. The team previously won the contest in 2013, 2014, 2016, and 2017.
“Our team’s success reflects our dedication to training the problem solvers of the future,” says Jon Cagan, interim dean of Carnegie Mellon’s College of Engineering.

“It's a fun way to learn and continue learning about computer security,” explained Hernandez , a 2014 INI graduate and six-time DefCon competitor. “It exposes you to new and exciting challenges in every competition, which means you are always learning about new topics whenever you play. It's also great to get hands-on experience which really helps cement the sorts of things we learn about in classes.”
PPP encourages new players to not be shy about seeking advice from veteran players. “It's important to find a team and engage with them,” Zarate said. “If you feel out of your depth, then sit in with someone that has more experience and ask questions!”
"Winning DefCon CTF has always been a team effort," added Hernandez. "There’s a lot of collaboration, sharing of knowledge, learning new skills and (sometimes) new architectures at this competition. It’s amazing to see how we come together as a team each year."

Team PPP
Back Row, Left to Right:
- Susie Chang
- Sam Kim
- Ricky Zhou
- Andrew Wesie
- Benjamin Lim
- Robert Xiao
- Max Serrano
- Tim Becker
- Jenish Rakholiya
- Richard Zhu
- Brian Pak
- Zach Wade
- Matthew Savage
- Carolina Zarate
- Ryan Goulden
- Artemis Tosini
- Ned Williamson
- Wong Wai Tuck
- Corwin de Boor
- Jay Bosamiya
- Erye Hernandez
- Tyler Nighswander