Using a Virtual Private Network at CMU
What is a VPN?
When a user browses the Internet, every site that is visited, button that is clicked, and information that is entered is traced back to the IP address of that device which is assigned by the Internet Service Provider (ISP). When connected to a VPN, the user’s public IP address is hidden from the world. Instead, the IP address shown is the one the VPN substitutes in its place.A VPN will mask the user’s IP address and provide some anonymity by creating a secure and encrypted private connection called a tunnel. This tunnel allows secure communications and the ability to extend local campus network access to off-site locations. As far as most websites are concerned, the user is browsing from the VPN server’s location, not the computer’s actual location.
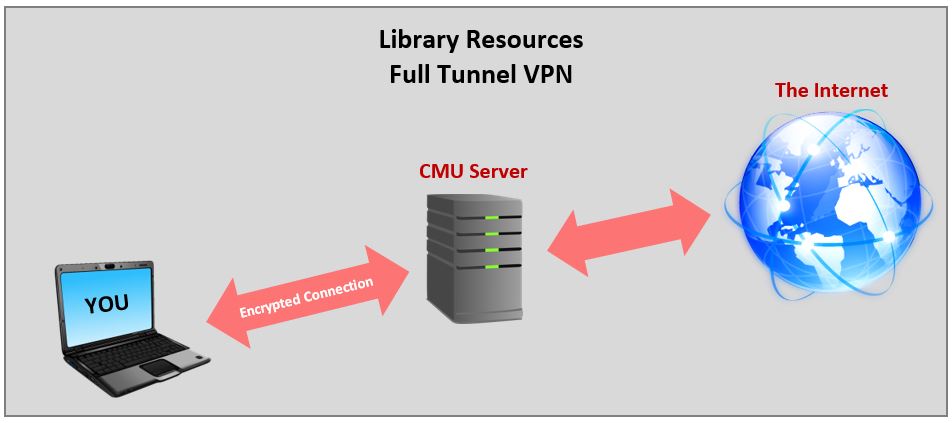
There are two modes that VPNs can operate in: fully tunneled, and split-tunneled. When a VPN is fully tunneled *all* traffic goes to the VPN server first, then out to the internet.
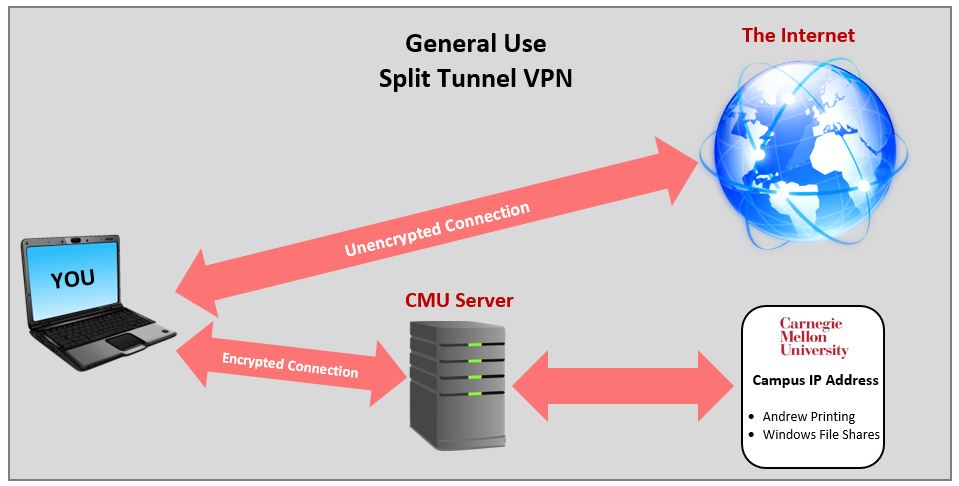
When a VPN is split-tunneled, only *some* traffic is encrypted to the VPN server first, all other traffic goes directly to the service(s) requested.
VPN at CMU
At Carnegie Mellon University, Cisco AnyConnect is the VPN client available for connecting to Carnegie Mellon’s VPNs. There are two primary VPNs available at CMU:- General Use Campus VPN- This split tunnel VPN will encrypt network traffic only going to campus IP addresses. You can access services on campus that are restricted to a campus connection (e.g. Windows file shares, Andrew printing)
- Library Resources VPN- This full tunnel VPN will encrypt ALL Internet network traffic and allows access to library resources such as research databases.
You will need a VPN connection for the following:
- Off-site access to an IP restricted service such as library databases
- Applications that do not provide secure transfer of data from off-campus
- Access to services on a restricted subnet
For more information on the Cisco AnyConnect VPN Client and instructions on how to download, please visit the Computing Services Virtual Private Networking webpage.